If you use a Palo Alto firewall, a new feature since PanOS 5.0 is the real time block lists. I’ve had a few people ask me how to set them up so here is the instructions.
To know what the max number of IPs that your firewall can handle in the RBL, run the following command from the CLI.
show system state | match cfg.general.max-address
This will give you the maximum number of IPs you can have in the list.
Next in the gui on your Palo Alto device, head to objects and then in the left, go to Dynamic Block Lists.
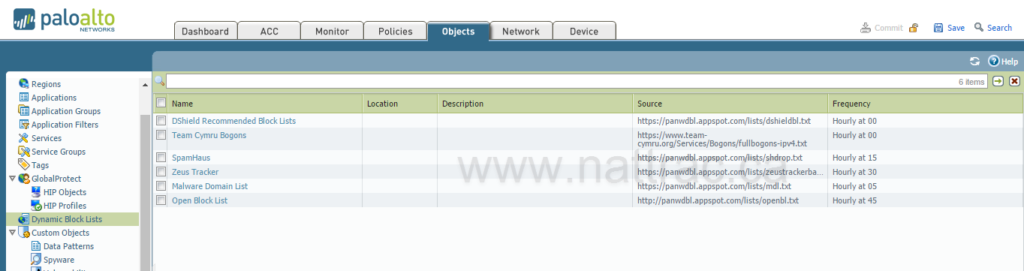
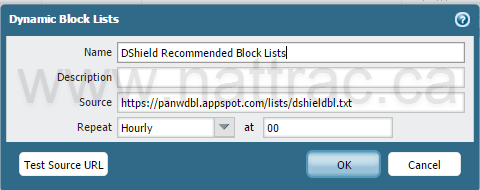
Here is the list of block lists that I’ve configured. To create a new one, click on the add button and give the list a name and a web source for the list. Decide how often you want it to update.
Finally you need to create a deny rule blocking these sites inbound.
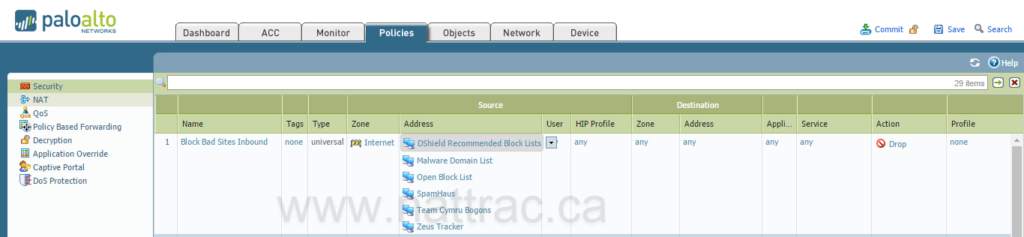
Commit the changes and you are off to the races. I often will leave logging on for a bit to see what is being blocked, but eventually, I turn it off because I don’t really care what traffic I am dropping.
Here is a list of sites I pull in. It appears some of these might be managed by a Palo Alto engineer, but I am not certain about this.
- DSheild Top 20 – https://panwdbl.appspot.com/lists/dshieldbl.txt
- https://www.team-cymru.org/Services/Bogons/fullbogons-ipv4.txt
- SpamHaus – https://panwdbl.appspot.com/lists/shdrop.txt (Spam list)
- Zues Tracker – https://panwdbl.appspot.com/lists/zeustrackerbadips.txt
- Malware Domain List – https://panwdbl.appspot.com/lists/mdl.txt
- Openblock List – http://panwdbl.appspot.com/lists/openbl.txt
